Blog
Why Every CISO Needs a Cyber Crisis Playbook (and Not Just a DR Plan)
Why Every CISO Needs a Cyber Crisis Playbook (and Not Just a DR Plan)
Cybersecurity regulation is tightening across the GCC, and CISOs are directly in the spotlight. In Saudi Arabia, for instance, the National Cybersecurity Authority (NCA) mandates not just technical safeguards but clear incident response protocols that include regulatory disclosures, communication workflows, and executive-level accountability.
A recent Global Compliance Survey found that 47% of surveyed executives identified regulatory complexity as the main factor that makes effective compliance more challenging. Yet most CISOs still rely on traditional Disaster Recovery (DR) plans that weren’t built to meet these evolving governance demands.
What’s missing is a structured, executive-ready cyber crisis management plan. You need a playbook designed not for recovery alone, but for real-time decision-making, stakeholder communication, and legal/regulatory exposure management.
Why DR Plans Aren’t Enough for Today’s Cybersecurity Threats
Disaster Recovery (DR) plans were never meant to handle the full spectrum of a cyberattack.
Following a targeted ransomware attack on a regional bank, operations stall. Email access is lost. Customer data is believed to be compromised. Within the first 30 minutes, the IT team initiates the disaster recovery plan. Backup servers are brought online. Network segmentation protocols are triggered.
But the real crisis has just begun.
The board is demanding an update. Legal is unsure if they are obligated to notify the regulator immediately. Customers are already posting on social media. And the executive team doesn’t know who is authorised to speak publicly.
The DR plan restores systems. It does not answer any of these questions.
And this is exactly where most organisations falter; not because their technical response is weak, but because they have not prepared for decision-making under pressure.
Modern cyberattacks, particularly those involving data loss, network infiltration, or cloud-based systems, necessitate more than just recovery. They require coordinated judgment from leaders across cybersecurity, legal, compliance, and communications. The absence of this coordination introduces delays, reputational harm, and in some cases, regulatory penalties.
A disaster recovery plan was never designed to handle such a situation. It addresses systems, not stakeholders.
To lead effectively, today’s CISOs must plan for the human, legal, and reputational dimensions of a cyber crisis. And that begins with acknowledging where DR ends—and where strategic response must begin.
What a Cyber Crisis Playbook Actually Solves
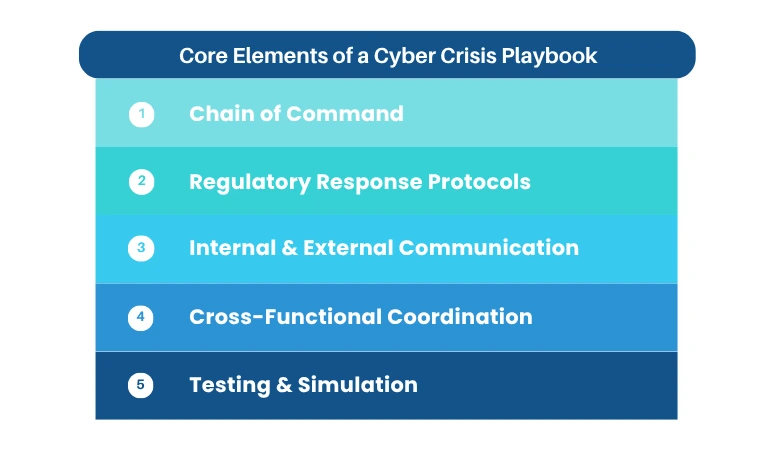
The cyber crisis playbook serves as the operational layer of leadership during an incident. While your DR plan restores systems, the playbook governs how your organisation reacts across legal, regulatory, and PR departments.
A mature playbook offers more than escalation paths. It provides tested response frameworks. Legal guidance under breach disclosure laws. Media holding statements. Regulatory notification templates. All of these are aligned in advance so that decisions can be made alongside system recovery, not after.
For organisations operating in regulated sectors like BFSI, healthcare, or critical infrastructure, a cyber crisis playbook is non-negotiable. The risk is not just downtime. It is public exposure, financial liability, and in some cases, criminal penalties for non-compliance.
It ensures that decisions aren’t made on the spur of the moment under pressure. Instead, roles are pre-defined, communication is controlled, and regulatory obligations are met without delays or internal conflict.
Measuring Operational Readiness: How to Test Your Cyber Crisis Playbook
The first time you deploy the playbook should not be in the face of a crisis when you are unaware of the weak points.
Crisis planning must move beyond documentation and into practice. CISOs need to know not just what’s written, but how people will respond under pressure. Hence, testing the playbook is an enterprise responsibility. Leadership, legal, communications, and compliance teams must be part of the process, not observers.
What happens when you haven’t tested the playbook
Thursday, 3:12 PM
A routine alert flags unusual activity on a privileged user account. At first glance, it appears to be credential misuse. Maybe internal. Maybe worse.
Your SOC escalates it within minutes. Forensics is still gathering evidence.
Decision Point 1: Do you inform leadership now, or wait for confirmation?
- If you escalate: Legal asks for a delay. PR isn’t ready. The CFO wants exact impact numbers.
- If you wait: The activity spreads. Files are being exfiltrated. You’ve lost 45 minutes.
No one is sure who makes the call.
4:05 PM
The breach is confirmed. Sensitive customer records were accessed.
The CEO wants a note drafted for the board. Legal reminds you of regulatory timelines. Comms is asking for a holding statement in case the media picks it up.
Decision Point 2: Who owns the next move?
Your DR plan is executing. Systems are coming back online. But every executive has a different priority, and no one has rehearsed this moment.
There’s no shared language. No agreed-upon chain of command. No clarity.
6:00 PM
The regulator contacts you before you report the breach. They’ve seen the same chatter that your comms team flagged an hour ago.
Internally, leadership is aligned only on one thing: confusion.
Externally, trust is eroding.
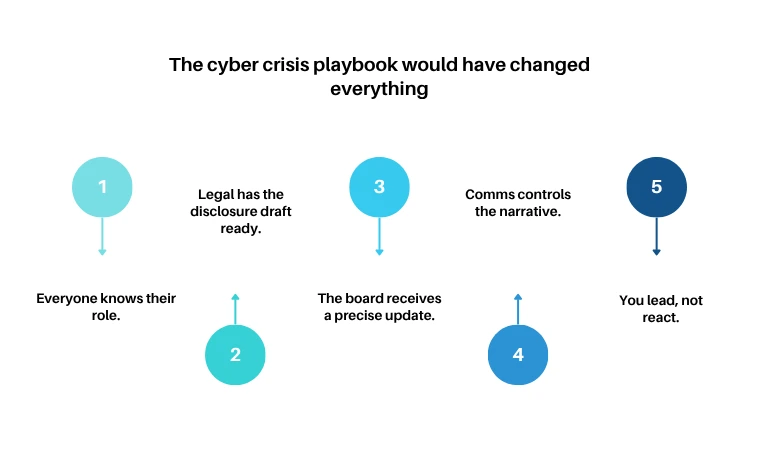
The cyber crisis playbook would have changed everything.
In a tested environment:
- Everyone knows their role.
- Legal has the disclosure draft ready.
- The board receives a precise update.
- Comms controls the narrative.
- You lead, not react.
This is what operational readiness looks like. And it doesn’t come from documentation. It comes from simulation.
Paramount’s Role in Crisis Preparedness
The role of Paramount Assure goes beyond cyber recovery. We prepare organizations to lead through cybersecurity challenges.
Our cybersecurity consulting practice in the UAE and wider GCC region is designed around governance, not just infrastructure. We help CISOs build and validate cyber crisis playbooks that align with:
- Regulatory requirements like NCA ECC, NESA, and sector-specific mandates
- Cloud computing security services and third-party dependency management
- AI governance frameworks for organisations adopting intelligent automation
- Cross-functional coordination between IT, legal, communications, and executive leadership
Our approach includes tabletop simulations, response maturity audits, and stakeholder workflow integration. This means your crisis response won’t be improvised; it will be rehearsed.
Because in a crisis, execution is what defines leadership.
Conclusion
Disaster recovery brings systems back online. However, only a playbook with a defined cyber crisis management plan can bring your organisation back under control.
For modern CISOs, that distinction matters. Regulatory scrutiny, public exposure, and board-level accountability all demand more than a technical response. They require tested, cross-functional readiness.
A well-prepared response isn’t just faster. It’s clearer, calmer, and trusted, because it’s been rehearsed.
Get in touch with Paramount to assess and operationalise your cyber crisis playbook.
Recent Posts
- AI with Effective Security for Organizations
- Building a Strong Human Defense Against Cyber Threats in the Middle East
- Everything You Need to Know About Passwordless Authentication
- Cloud Migration Strategy: A Step-by-Step Guide for Middle Eastern Enterprises | Paramount
- How to Implement Identity & Access Management (IAM) Easily?

Protect your online assets from cyber threats with Paramount

Comprehensive cyber security solutions for individuals and businesses

Significantly reduce the risk of cyber threats and ensure a safer digital environment.